Amrisha Prashar
on 4 February 2016
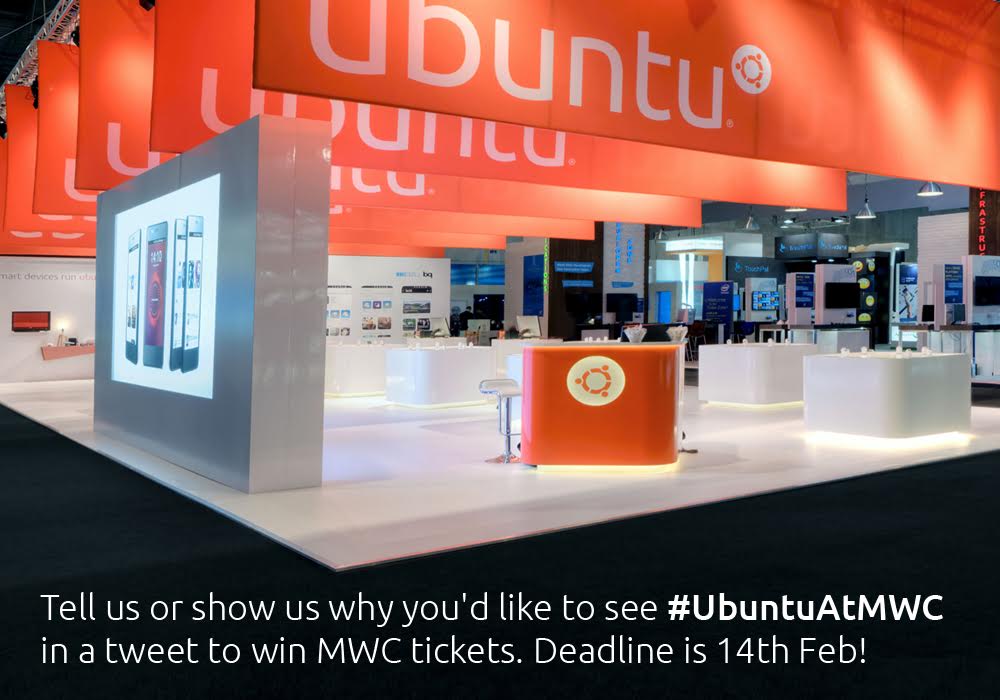
We’re really excited about MWC this year and can’t wait to showcase the various demos across Cloud and Devices!
For those of you not going we’d love to offer you the chance to come and join us and see what we have on display – as our presence is even bigger and better than last year.
To win tickets to MWC we’d like you to tell us or show us why you want to see Ubuntu at MWC in a tweet! Feel free to be as creative as possible with text, images, GIFs or even videos and add the hashtag #UbuntuAtMWC so we can track your awesome entries. The competition starts on 4th Feb (17:00 GMT) and finishes just before the stroke of midnight on Valentines day – 14th Feb (23:55 GMT.) Our creative team will judge the entries based on originality and select three winners where we’ll contact you via Twitter.
Happy creating and we can’t wait for your entries!



